This year we decided to provide security focused modules and content for the holiday season. These are parts of the security configuration we implement on our own infrastructure, based on OpenSCAP and other sources. By putting these into easy to use modules and writing about it, we hope to give our community of users something valuable: Educational and easy to understand security tips, along with configuration which can quickly be automated across your entire infrastructure, using CFEngine. Today, at the seventh day of the calendar, we will share a summary of the first week.
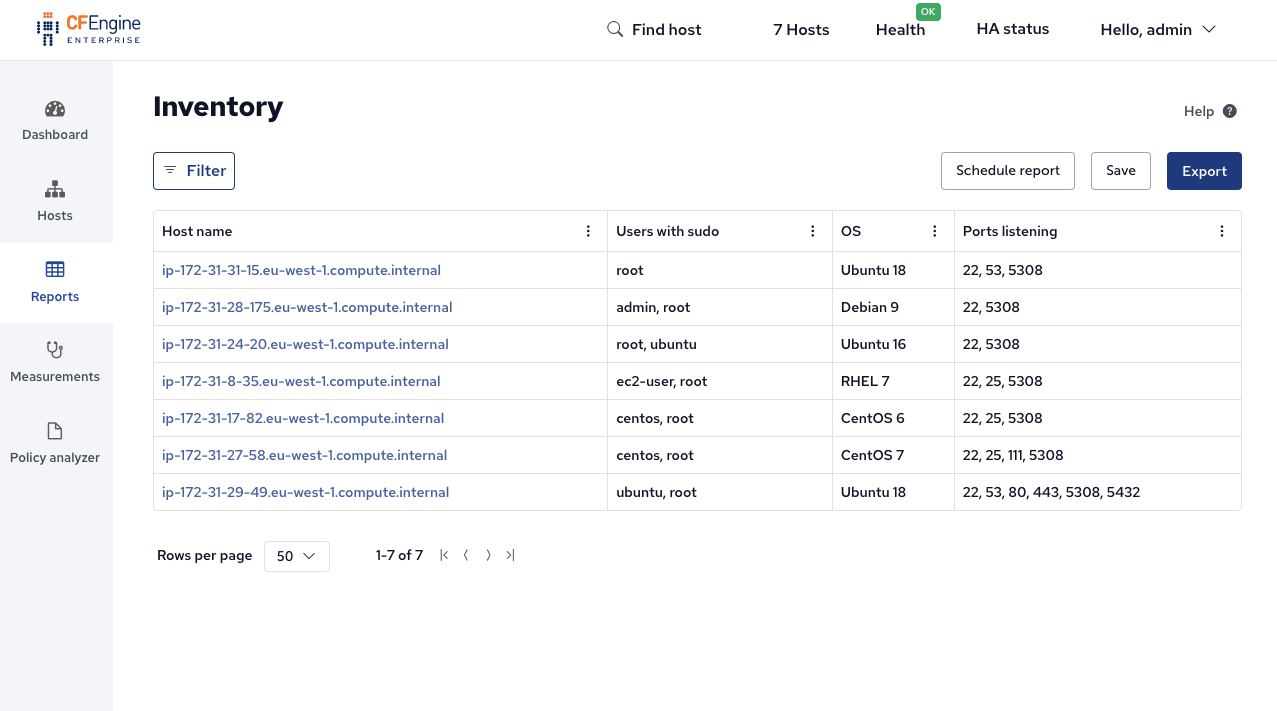
Reports of all local users with sudo access (1/25)
sudo enables you to run a command with elevated privileges. You should monitor and restrict who is allowed to use it:
build.cfengine.com/modules/inventory-sudoers
This module provides the attribute Users with sudo which can be added to inventory reports:
Recommendation: Review this list on a regular basis, and ensure all of the users really need sudo access.
Remove sudo access where possible by editing the /etc/sudoers file.
Use SHA-512 to hash passwords by default (2/25)
MD5, DES, and other older algorithms are no longer secure, and shouldn’t be used for any cryptographic purposes. Use a better default, like SHA-512:
build.cfengine.com/modules/default-encrypt-method-sha512
Running CFEngine with this module in your policy set on a system which uses MD5 looks like this:
$ cat /etc/login.defs | grep '^ENCRYPT_METHOD'
ENCRYPT_METHOD MD5
$ cf-agent -KI
info: Replaced pattern '^\s*(ENCRYPT_METHOD\s+(?!SHA512$).*|ENCRYPT_METHOD)$' in '/etc/login.defs'
info: replace_patterns promise '^\s*(ENCRYPT_METHOD\s+(?!SHA512$).*|ENCRYPT_METHOD)$' repaired
info: Edited file '/etc/login.defs'
$ cat /etc/login.defs | grep '^ENCRYPT_METHOD'
ENCRYPT_METHOD SHA512Recommendation: Don’t use MD5 or other insecure hashing algorithms. Use this module to enforce a strong default across your systems. Look into what other places you might be relying on outdated cryptographic algorithms and how you can eliminate them. (See for example FIPS mode).
Disable root login over SSH (3/25)
SSH allows you to securely log into a remote machine and run commands there (in a shell). Attackers will commonly try to log in as root, since the root user exists almost everywhere, and generally has a lot of access. It is a good idea to disable this completely.
build.cfengine.com/modules/ssh-permit-root-login-no
This module ensures that the SSH daemon (sshd) does not permit logging in with the root user account.
There are several reasons why allowing this could be problematic, from a security perspective:
- It is a good target for attackers, to try logging in as
root:- The
rootuser exists on almost all UNIX-like system. - The
rootuser normally has a lot of privileges (access), to read data or change the system. - Sometimes the
rootuser has a default / insecure password.
- The
- The
rootuser is not personal.- When people log in with root you cannot know who did what, or effectively restrict access based on person / role.
Recommendation: Ensure logging in with SSH as root is not possible.
This can be achieved by adding this module to your policy set and deploying it to all your infrastructure (via the policy server).
Due to the reasons above, this is beneficial, even if you allow users to become root after they log in.
Uninstall telnet-server package (4/25)
Telnet is a protocol for providing remote terminal access to hosts over network. It is generally considered obsolete and dangerous. The first step to make sure it’s not used, is to make sure it’s not installed.
build.cfengine.com/modules/telnet-server-not-installed
Example of a cf-agent run on a host that has the telnet-server package installed:
[root@hub]# cf-agent -KI
info: Successfully removed package 'telnet-server'Recommendation: Ensure it is not possible to use telnet to log into your machines. This can be achieved by using this module, which uninstalls the telnet server if it is installed.
Reports of kernel boot parameters (5/25)
What parameters are used to boot the Linux kernel can affect performance, functionality and security. Seeing the configuration of all your servers allows you to detect misconfigurations and fix them.
build.cfengine.com/modules/inventory-kernel-boot-params
This module makes CFEngine report a new inventory attribute, Kernel Boot Params:
Recommendation: Use this module to get up to date reports of the Linux kernel boot parameters used in your infrastructure. Review them and look for misconfigurations or outliers.
Security checks with Lynis (6/25)
Lynis is a security tool for hosts running Linux, macOS, or other Unix-based operating systems. It performs an extensive health scan of your host to support system hardening and compliance testing.
build.cfengine.com/modules/lynis
This module will automate installation, running and reporting of Lynis results, on all UNIX-like hosts you have in CFEngine.
If used from the command line, you can add the --info option to see all the results from Lynis:
$ cf-agent --no-lock --info
R: ----- Warnings -----
R: NETW-2704 -- Nameserver 192.168.1.1 does not respond
R: PKGS-7392 -- Found one or more vulnerable packages.
R: NETW-2705 -- Couldn't find 2 responsive nameservers
R: ----- Suggestions -----
R: NETW-2704 -- Check connection to this nameserver and make sure no outbound DNS queries are blocked (port 53 UDP and TCP).
R: KRNL-6000 -- One or more sysctl values differ from the scan profile and could be tweaked
R: HRDN-7222 -- Harden compilers like restricting access to root user only
R: PKGS-7392 -- Update your system with apt-get update, apt-get upgrade, apt-get dist-upgrade and/or unattended-upgrades
R: ACCT-9626 -- Enable sysstat to collect accounting (no results)
R: MACF-6208 -- Check output of aa-status
...Recommendation: Run Lynis on all UNIX-like hosts in your infrastructure. Investigate the results and fix as much as possible. Learn more about Lynis on their official website.
SSH authentication attempts (7/25)
Attackers can try to log in to SSH many times, testing different passwords. To stop this, you can configure the SSH daemon with a maximum number of attempts:
build.cfengine.com/modules/ssh-max-auth-tries
This module looks at the SSH daemon configuration in /etc/ssh/sshd_config.
If the MaxAuthTries parameter is not already set to the correct value (3, by default), the necessary changes will be made:
- Backup the config
- Edit the config
- Replace old config with new config
- Restart SSH daemon
Recommendation: Stop brute-force attacks which try to authenticate many times with SSH by limiting the number of possible attempts. You can achieve this by adding the module to your policy set, and it will be enforced on all hosts you have in CFEngine.
Subscribe to the calendar
This is just the beginning, we have 18 days left! To sign up and receive daily security hardening content through Dec. 25th, use this link.